Backdoor.Orcus
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 3,988 |
| Threat Level: | 60 % (Medium) |
| Infected Computers: | 3,846 |
| First Seen: | July 6, 2016 |
| Last Seen: | September 19, 2023 |
| OS(es) Affected: | Windows |
Backdoor.MoSucker (also known as Backdoor.Orcus) is a generic Trojan that threat actors deploy to users via exploit kits and spam emails. The Backdoor.MoSucker Trojan features the same capabilities you can find in remote access tools like TeamViewer and LogMeIn with added functionality. The Backdoor.MoSucker program can be used by threat actors to kill, run and modify processes on the infected system. Backdoor.MoSucker can move, rename and delete files on the local disk. The Trojan can log the user's activity and change the desktop background image. Also, the malware can be instructed to show message boxes, change data & time properties, restart the PC and modify the Windows Registry.
The Backdoor.MoSucker Trojan is configured to maintain a constant connection to its 'Command and Control' servers as long as the infected machine is turned on. Compromised users may notice strange movements of their mouse cursor and keyboard input that is not consistent with their commands. Backdoor.MoSucker can restrict the user's ability to issue commands to the compromised system and transform the device into a proxy for a remote user's advantage. Infected machines may be used to hide the network traffic of threat actors and even execute DDoS (Distributed Denial of Service) attacks. It is advised to remove the Backdoor.MoSucker Trojan in offline mode using a trusted anti-malware scanner.
Detection names for Backdoor.MoSucker by AVs:
BKDR_MOSUCK.A
BackDoor.Mosu
Backdoor.Generic.180860
Backdoor.Win32.MoSucker.dd!IK
Backdoor.Win32.Mocbot.bn
Heuristic.LooksLike.Win32.Spypro.B
Packer.Morphine.Gen (v)
TR/Crypt.Morphine.Gen
TrojWare.Win32.PkdMorphine.~AN
W32/Troj_Obfusc.Z.gen!Eldorado
Win-Trojan/Mosucker.75506
Win32:MoSucker-N [Trj]
Table of Contents
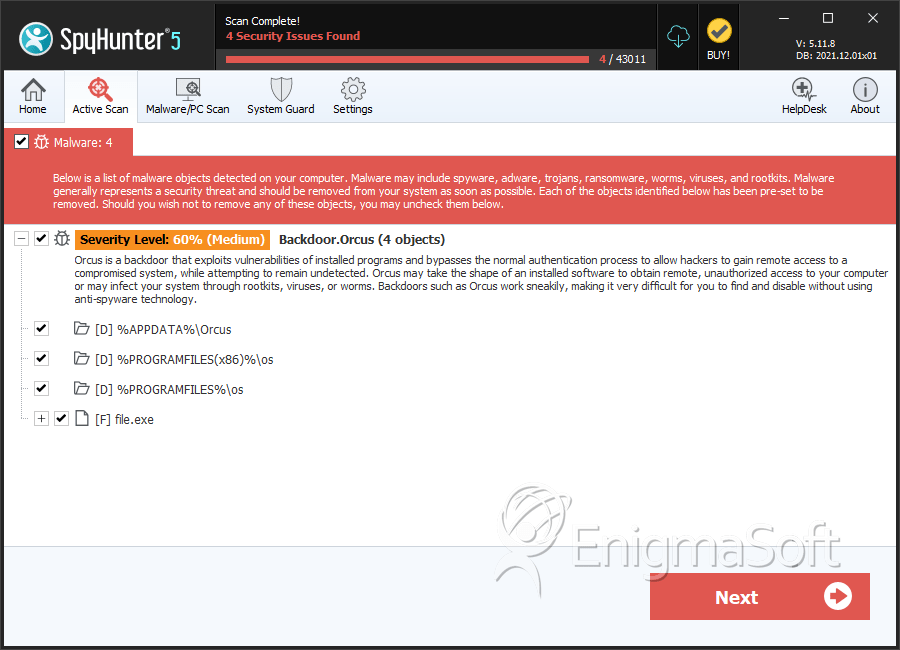
SpyHunter Detects & Remove Backdoor.Orcus
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 956098914ea294ef80ed87da2dae7eda | 0 |
Registry Details
Directories
Backdoor.Orcus may create the following directory or directories:
| %APPDATA%\Orcus |
| %PROGRAMFILES%\os |
| %PROGRAMFILES(x86)%\os |

