Celas Trojan
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 16,391 |
| Threat Level: | 90 % (High) |
| Infected Computers: | 2 |
| First Seen: | May 22, 2012 |
| Last Seen: | July 11, 2023 |
| OS(es) Affected: | Windows |
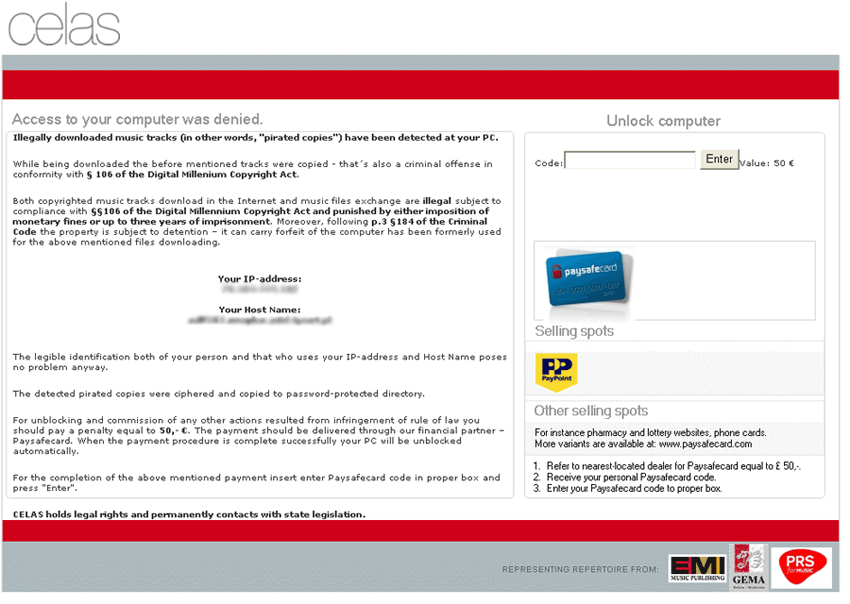
Celas Trojan Image
The Celas Trojan is a ransomware Trojan that uses a typical Winlocker approach to take over your computer. This Trojan's main strategy entails preventing you from using your computer by blocking access to Windows and displaying a message demanding the payment of a ransom. This kind of message is different depending on the ransomware attack. For example, some ransomware Trojans will claim to have been sent by law enforcement, claiming that your computer was involved in child pornography traffic while others will claim that your computer's information was locked down for 'your safety' because it was infected with a particularly dangerous virus.
Table of Contents
The Celas Trojan’s Message
The Celas Trojan's message will say that your computer contains copyrighted audio files that were copied illegally. Since copyright laws regarding music have always been murky, this may actually be true if you have ever ripped a CD or downloaded a mp3 file online. However, it is important to note that the Celas Trojan is not associated with law enforcement in any way and that this message is just there to scare you into paying a fifty euro ransom.
Do Not Pay the Celas Trojan’s Ransom
Like the majority of the ransomware infections active today, the Celas Trojan will demand payment via Ukash or PaySafeCard. These are both legitimate money transfer services that are not involved with the Celas Trojan or other malware. The Celas Trojan message contains a section where you can enter your payment code after you pay the ransom. However, ESG malware researchers recommend against believing the Celas Trojan's message and paying its ransom. Apart from being a waste of your money, you have no guarantee that the criminals behind the Celas Trojan will actually disable this ransomware infection once you have paid the ransom.
Removing the Celas Trojan from Your Computer
A fully updated anti-malware program should be able to remove the Celas Trojan with few problems. However, the main issue with removing a ransomware infection is gaining access to your computer system in the first place. After all, how can you access your anti-malware software if the Celas Trojan blocks access to your desktop, Task Manager, command line, and other Windows components? Fortunately, you can bypass the Celas Trojan message by starting up your computer system from an alternative boot source (such as an external memory drive) or, in some systems, by starting up in Safe Mode.
File System Details
| # | File Name |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 1. | %AppData%\[RANDOM TROJAN NAME].exe | |
| 2. | %StartupFolder%\wpbt0.dll | |
| 3. | %StartupFolder%\ch810.exe | |
| 4. | %AppData%\[RANDOM TROJAN NAME]\toolbardtx.ini | |
| 5. | %AppData%\[RANDOM TROJAN NAME]\toolbarguid.dat | |
| 6. | %AppData%\[RANDOM TROJAN NAME]\toolbarstats.dat | |
| 7. | %AppData%\[RANDOM TROJAN NAME]\toolbarstat.log | |
| 8. | %AppData%\[RANDOM TROJAN NAME]\toolbarpreferences.dat | |
| 9. | %AppData%\[RANDOM TROJAN NAME]\toolbaruninstallIE.dat | |
| 10. | %AppData%\[RANDOM TROJAN NAME]\toolbarversion.xml | |
| 11. | %AppData%\[RANDOM TROJAN NAME]\toolbarlog.txt | |
| 12. | %AppData%\[RANDOM TROJAN NAME]\toolbaruninstallStatIE.dat |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.