CryptoWall Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 16,010 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 4,825 |
| First Seen: | May 12, 2014 |
| Last Seen: | April 8, 2024 |
| OS(es) Affected: | Windows |
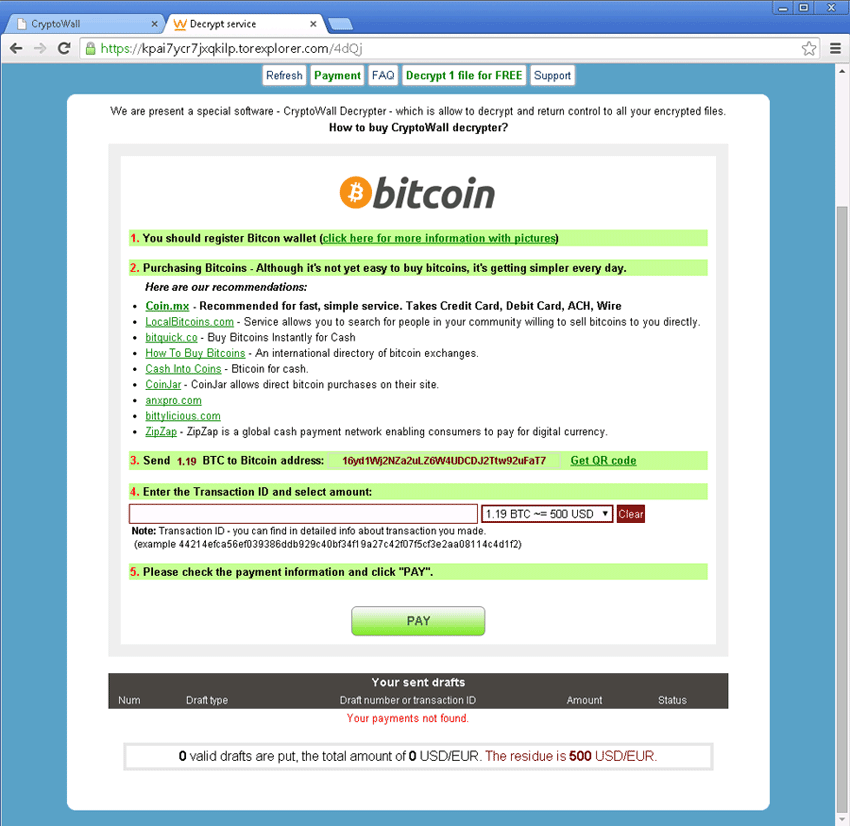
CryptoWall Ransomware Image
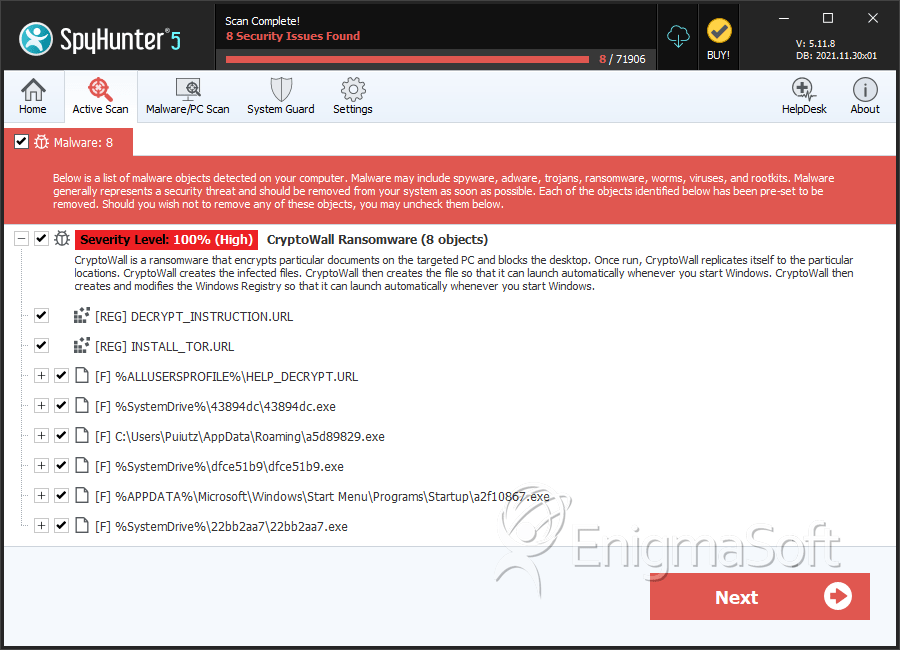
The CryptoWall Ransomware is a ransomware Trojan that carries the same strategy as a number of other encryption ransomware infections such as Cryptorbit Ransomware or CryptoLocker Ransomware. The CryptoWall Ransomware is designed to infect all versions of Windows, including Windows XP, Windows Vista, Windows 7 and Windows 8. As soon as the CryptoWall Ransomware infects a computer, the CryptoWall Ransomware uses the RSA2048 encryption to encrypt crucial files. Effectively, the CryptoWall Ransomware prevents computer users from accessing their data, which will be encrypted and out of reach. The CryptoWall Ransomware claims that it is necessary to pay $500 USD to recover the encrypted data. The payment is demanded using TOR and Bitcoins in order to maintain the recipients' anonymity. Malware researchers strongly advise against paying the CryptoWall Ransomware ransom. This only encourages ill-minded persons to continue carrying these types of attacks and does not guarantee that you will recover your data.
Table of Contents
Fake Updates and Spam Emails may Bring the CryptoWall Ransomware to Your Computer
The CryptoWall Ransomware is distributed as a fake update for applications such as Adobe Reader, Flash Player or the Java Runtime Environment. These types of updates may be offered in pop-up windows when you visit unsafe websites or when a Potentially Unwanted Program is installed on your computer. The CryptoWall Ransomware also may be distributed using spam email attachments and other typical threat delivery methods. Apart from encrypting your software, the CryptoWall Ransomware will also drop the files DECRYPT_INSTRUCTION.txt, DECRYPT_INSTRUCTION.html and DECRYPT_INSTRUCTION.url into directories where the CryptoWall Ransomware has encrypted data. The CryptoWall Ransomware uses the following ransom message to demand payment:
Decrypt service
Your files are encrypted.
To get the key to decrypt files you have to pay 500 USD/EUR. If payments is not made before [date] the cost of decrypting files will increase 2 times and will be 1000 USD/EUR Prior to increasing the amount left: [count down timer]
We are present a special software - CryptoWall Decrypter - which is allow to decrypt and return control to all your encrypted files. How to buy CryptoWall decrypter?
1.You should register Bitcoin waller
2. Purchasing Bitcoins - Although it's not yet easy to buy bit coins, it's getting simpler every day.
3. Send 1.22 BTC to Bitcoin address: 1BhLzCZGY6dwQYgX4B6NR5sjDebBPNapvv
4. Enter the Transaction ID and select amount.
5. Please check the payment information and click 'PAY'.
Avoid paying this ransom. Instead remove the CryptoWall Ransomware using a reliable, fully updated security program and then recover your files from an external back-up.
SpyHunter Detects & Remove CryptoWall Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | HELP_DECRYPT.URL | a8f62bf5921bc682767ba649abb0ce9f | 160 |
| 2. | HELP_DECRYPT.URL | 4d565d1d01c01f4edc7c96eb39e93cab | 95 |
| 3. | HELP_DECRYPT.URL | 08ea8970f1593d049dd00dca7d535c04 | 72 |
| 4. | HELP_DECRYPT.URL | 68bab4a48588991342ca900e7b3db1d8 | 54 |
| 5. | HELP_DECRYPT.URL | 47bb7af1940f80b1477a4430f576701e | 47 |
| 6. | HELP_DECRYPT.URL | d606f907a0ecd1c6284b8403163db19a | 31 |
| 7. | HELP_DECRYPT.URL | f334d225e7b69922a4b6d721cffd9e5b | 29 |
| 8. | HELP_DECRYPT.URL | 122b42b69934ad0b048b4b33975a6e27 | 24 |
| 9. | HELP_DECRYPT.URL | 7c60e7ae33a9252175c0aa1f4cf48b49 | 24 |
| 10. | HELP_DECRYPT.URL | 50c4e43fd6915c1a9cddee1ee66c302f | 24 |
| 11. | HELP_DECRYPT.URL | 44eacd73cfd0dbee7a8f048baf511d76 | 20 |
| 12. | HELP_DECRYPT.URL | ba16fa3553de2faee012711ee3be95ca | 18 |
| 13. | HELP_DECRYPT.URL | e1354965ef0a094c0a108c8f4beaf894 | 17 |
| 14. | HELP_DECRYPT.URL | 8f31b9d3ff75e986362141cbe148c867 | 17 |
| 15. | HELP_DECRYPT.URL | e33aeb80de3075fa61ab0e262d04ec2e | 17 |
| 16. | HELP_DECRYPT.URL | 5ee50f380144d576e13d5ccc9d173939 | 17 |
| 17. | HELP_DECRYPT.URL | b03ea0395f99158ee20e1125f0722a6a | 17 |
| 18. | HELP_DECRYPT.URL | cdba5dc46a9aa9beec7f583d24006fa9 | 17 |
| 19. | HELP_DECRYPT.URL | bfbb39ddb1bc96d2314e2bb6c401a9ac | 15 |
| 20. | HELP_DECRYPT.URL | 7ab7c8e43de679951430475a2868c532 | 11 |
| 21. | HELP_DECRYPT.URL | 9e776be5adb8442bb77346df48a923f1 | 10 |
| 22. | HELP_DECRYPT.URL | ec022b5fdf508e1412110aa890e0158c | 9 |
| 23. | a5d89829.exe | edfeb771395e1807109712a2bf158599 | 5 |
| 24. | DECRYPT_INSTRUCTION.html | ||
| 25. | DECRYPT_INSTRUCTION.url | ||
| 26. | DECRYPT_INSTRUCTION.txt |
